1. Introduction
ore than a century ago, Warren & Brandeis have defined privacy as "the right to let alone" and their concern about privacy was quite prompted [1] . The emerging ambiguity in information society has raised many privacy and trust issues that are context dependent. These issues will pose many challenges for policy-makers and stakeholders because people's notion of privacy and trust are different and shifting [2] . Policies are considered as a fundamental factor to provide security and privacy in applications such as, file sharing, web browsing, web publishing, networking, and mobile computing. Such applications demand highly accurate policies to ensure that resources remain available to authorized access but not prone to compromise. The policies of the past are not suited to deal with new challenges and we are probably entering into new era that would require developing more effective policies. There are lots of uncertainties & risks today concerning our privacy & trust. It is also seen that people are sometimes compelled in circumstances to surrender their personal data to gain something [2] . Two non-expert groups of policy authors are on the rise. First are the non-technical enterprise policy authors, typically Author: Member IEEE, Oslo Norway. e-mail: [email protected] lawyers or business executives, who have the responsibility to write policies governing an enterprise's handling of personal information [3] . Second are endusers, such as that wish to set up their own spam filter, share photographs, videos or important files with friends but wants to protect them from un-authorize access [4] . It is important to continue researching better mechanisms for security & privacy policies authoring and to establishing good guidelines; because to achieve the best security goals it's crucial to obtain high quality to ensure the intended policy. This work shows the current role of privacy policy in policy management, but it is still immature in making security analysis and assessments [5] . Furthermore with this research, the interest to make the organizations flexible with respect to privacy matters, consistent over the design of policy language that could be enforceable.
2. II.
3. Background Realities and Issues
This section is laid down to get a good basis for specifying the ground of this area and creates a sense about the level of clients` concerns on privacy policy.
4. a) What are privacy policy and security trust issues?
Privacy policies are meant to protect the privacy of the user: they need to reflect current regulations and possibly promises made to the customers. "A privacy policy is a legal document that discloses some or all of the ways a party gathers, uses, discloses and manages a customer's data. The exact contents of a privacy policy will depend upon the applicable law and may need to address the requirements of multiple countries or jurisdictions" [6] . While there is no exact universal guidance or recommendations for the content or text of specific privacy policies, a number of organizations provide example forms, templates or online consultant for this purpose [6] . Privacy policies arise further issues in comparison to access control policies, as they require a more sophisticated treatment of deny rules and conditions on context information; moreover privacy policy languages have to take into account the notion of "purpose", which is essential to privacy legislation [7] . "A subset of privacy policies are enterprise privacy policies which furthermore have to provide support to more restrictive enterprise-internal practices and may need to handle customer preferences" [7] . This means that an enterprise level privacy policies plays a vital role to increase the loyalty with the users.
5. Year ( )
H b) Is a policy context difficult with typical legal jargon? Many researchers of system security are asking the question; why do few people read the privacy policies [8] . One common fact is simply that policies are often written in a hard and complicated language which a common user or subscriber cannot understand [8], [9] . In privacy notice research conducted by [10] the research is conducted in 2001 and in that research, 29 percent of the respondents expresses their feelings that policy contents are very difficult to read and 45 percent of respondents said that it was difficult to understand them. Another good reason subscribers have given for not understanding the policy is that they contain a lot of legal and lawful jargon [10] . In the survey by Milne [11] , about 53 percent of the respondents agreed, or strongly agreed to, that privacy notices often use legal language which is very hard to understand or is confusing for most people. Same as described in [12] those policies use certain statement and distinct vocabularies which made them very hard to understand, even for the experienced reader.
6. c) What is the standardization of policy context?
Lack of standardization of privacy policy contents is also a problem. Different websites use different ways for structuring the information in their policies. Many service operators claim that their security statement first explains what particular information they are collecting and then how they will use those details [13] . Other service operators tells where on the website they would collect personal information, and then explain what they will do to protect this information [13] . Some service operators post on their website F.A.Q (Frequently Asked Questions) format focusing on answering the most common questions that mostly asked by the users regarding their privacy [13] . There is no particular standardization adopted across the organizations / companies for comparison [12]. The ability to compare policies could be helpful in many situations (e.g. where users have a chance to select a company /organization to fulfil its requirements on privacy and security).
7. d) What are the main privacy concerns?
The privacy threats of which people are concerned include;
i. Visit to the websites will be tracked secretly without informing the user [16] . ii. E-mail Id`s and other official information will be stored and used for marketing, publicity and other similar purpose without permission of the user [16]. iii. Personal information will be sold to third parties without getting permission from user [16] . The advances of internet & database technologies increase information privacy threats. Data entered into forms or contained in existing databases, can be combined almost effortlessly with banking transaction records, and records of a user's every click of a mouse on internet. Privacy concerns increase further as data mining tools and services become more widely available [17] . There is a potential for fraudulent activities on the internet, as few regulatory standards exist [18] . The security of banking card information for online purchase is also incorporated with the privacy concerns. Amazon.com admitted that hackers undetected over four months have stolen about 98,000 bank card numbers. Hackers from time to time publish a list of stolen card numbers and related information over the internet [18] . The information without permission may lead to a fraud, which has very serious consequences [17] . Although personal information may not be used after collecting them, it must be noticed that keeping information is a liability for a website when it meets some good consumers or some old users that take the safeguard of their privacy seriously. The Internet based businesses should take good care of the privacy concerns because the common consumer does not really care about going through every line of policy context. Surveys show that people are more comfortable if they see privacy statement has been approved by a third party, such as Trust-E [19], [20] .
8. e) How client`s trust on security policies?
Just like other studies have discussed on users` trust on privacy statements, a study conducted by [21] also discovered that respondents were most willing to provide information with a strong privacy statement. Based on the responses for providing personal information, it appeared that many Internet users would be unwilling to provide personal information online, except when offered a strong policy statement. In this context, the importance of the privacy policy becomes apparent. It is the only way a website can communicate privacy issues with the users. The article [21] concludes by showing strong concern for the low percentage of policy readers, given the impact that such statements would purportedly have on consumer trust. It has however been found that consumer trust relies on other aspects than the privacy policy. Studies have found that users tend to not read the whole privacy policy because they gained trust to the company through previous experience [22] . Almost half of the respondents in the study by [11] agreed or strongly agreed; when asked if they did not read the privacy policy because of pervious offline experience with a company and just 25 % disagreed. Similarly in the same study 45% agreed that they do not read the policy contents if it belongs to a well known organization or by a well repudiated service provider. In a 2000 survey, about 66% responded that they got increased confidence in a site if a privacy policy was present [23]. In other words, by just seeing a privacy policy posted some users may believe that the sites they are visiting are safe in terms of privacy. They may also naively believe that "a security policy exposes a website to
9. Global Journal of C omp uter S cience and T echnology
Volume XV Issue I Version I Year ( ) H potential legal action; a website will always adhere to its policy" [23] . These findings can be related to that some users believe policies are all the same, look like and have same context and that just by seeing it posted could make them believe its content is similar to other polices.
10. III.
11. Primary Privacy Principles
We will see that different approaches to regulate privacy protection has led to a global patchwork of privacy laws, regulations and enforcement mechanisms which vary greatly from state to state, region to region , adding complexity to the privacy landscape. Many of the laws and regulations enforced today do however have something in common which is that they are based on privacy principles and guidelines developed over past 40 years. a) Fairness and lawfulness: This principle implies that personal information should be handled fairly and lawfully. Behind this important principle is a requirement that the data controller should respect and take into consideration the data subject's interests and reasonable expectations. The data subject should not be forced to submit personal information or to accept that this information is used to other specific purposes [24] .
12. b) Limitations on collection:
The basic purpose of this principle is to limit the amount of data collected to what is necessary to carry out further processing of the data which corresponds with OECD's collection limitation principle. In [24] the authors mention that there is not enough reason that the information is useful, the information must be necessary. The further processing of data should correspond with the purpose of which the data was collected for [24] . c) Purpose binding: This principle means that personal information should be handled to a stated, legitimate purpose and should be handled to this purpose only. The purpose should be stated in a reasonable accurate way not later than at the time the information is collected, which complies with the purpose specification principle and the use limitation principle of OECD [24] . d) Quality of the information: This principle is concerning the quality of the information. The information should be correct compared to what the information is supposed to represent [24] . The information should also be relevant, adequate and complete based on the purpose of which the information is to be used, and to be up to date, which correspond with the data quality principle of OECD [24] . e) The co-determination: This principle implies that the data subject should to a certain degree be able to participate and influence other`s processing of information concerning it [24] . Persons can decide themselves if personal information about them is to be collected by others and for what purpose, unless the collection is done by the legal authority. This implies that persons can oppose to some types of processing of personal data, such as personal marketing etc [24] .
f) Security safeguards: The confidentiality and integrity of personal data should be protected by reasonable security safeguards. Confidentiality here means protection of personal data from unauthorized access or disclosure, and protection of integrity means protection against unauthorized destruction, use and modification of personal data [24] . g) Data sensitivity: Certain types of personal information are more sensitive for the data subject than other personal information. This is mostly information concerning the data subject's health, sexuality, race or ethnical background, political, religious or philosophical opinions, or memberships in certain type of organizations (e.g. Trade agreements, unions, joint business strategies etc).
13. IV. Methodology and Evaluating Results
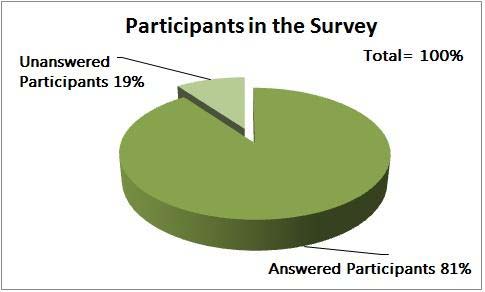
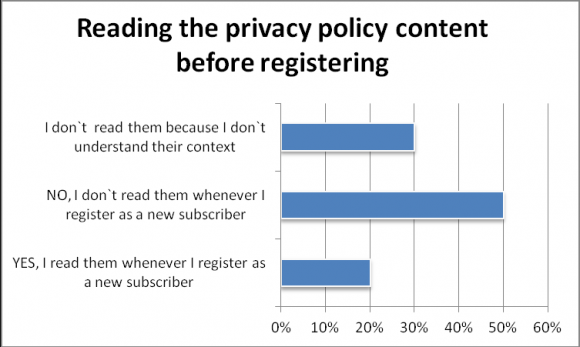
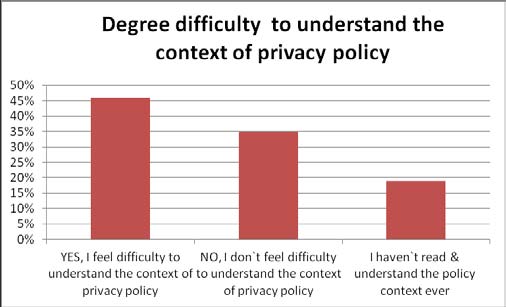
We circulated a questionnaire to the peoples that are working & living in Norway. This response was collected by sending 4 times reminder on different working days via email and messages to fill out the survey. Approximately, 81 percent incorporate their opinions about the privacy and security issues that have risen in this research. About 19 percent rejected or did not try to record their response. Around 30% of the respondents don`t read the context because they don`t understand them or has no time to read the policy before getting registered. Only 20% of the respondents have voted that they read the contents of the privacy policy when they are registered as a new subscriber. The basic purpose of this question was to analyze how important a privacy policy for a subscriber, whenever they register and give their personal information to the service provider. In this question we have asked from our survey participants how difficult they feel when they read the policy content. By looking at fig 5, shockingly majority (46%) of the total respondents are feeling problem in understanding the content of the privacy policy. 19% of the respondents have informed us that they have not ever read & understand the privacy context before using the services. Lastly, just 35% of the respondents do not feel any difficulty in understanding the context of the privacy policy.
14. Global Journal of C omp uter S cience and T echnology
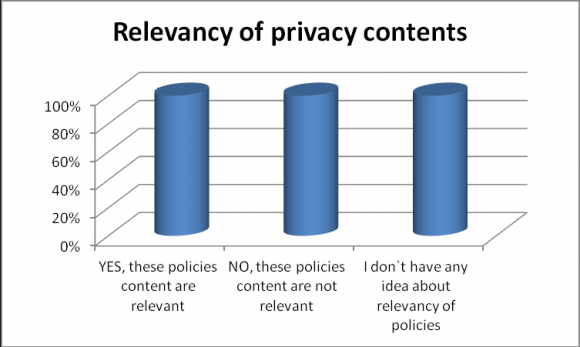
Volume XV Issue I Version I Year ( ) of the respondents agreed that they are not at all relevant from them. Around 30% of the respondents says that policy contents are useful whenever they registered and relevant for them. Finally we can see that round about 28% of the survey respondents has no any idea about the relevancy of these privacy policies from the subscriber point of view. We have asked from our participants to what extent they are confident enough to give their personal information to a service provider. We analyzed the results as shown in fig 7 that 81 percent of the respondents are not confident to give their personal information to the service provider and just 19% of the respondents are confident to give their personal information to the service provider. Finally, we have asked from our participants that whether they are aware whenever their service operator amends the privacy policy on website or on any other platform of communication.
The results are given in fig 8. It was shocking that majority of the respondents (81%) are not aware when there is any amendments performed by their service provider. According to our research survey just 19% of the respondents are aware when there are any amendments from the service provider.
V.
15. Limitations & Trends
As seen from our evaluations, future approaches to alternative ways of presenting privacy policy are quite limited. While the idea of a unified policy and regulation on the topic of privacy and is unlikely to ever happen. The development of data protection laws throughout the globe is promising, and could create a better foundation of taking the user into confidence, and creating innovative ways of presenting privacy policies in the future. There have, however, emerged several interesting topics regarding privacy policies through this online web survey, and especially the different aspects that defines user confidence in sharing online information seems fruitful to base future research on. Further analysis in modifying the version of privacy seals could also be interesting to investigate further. Being a self-regulatory approach, the idea of how this approach could effectively work in the context of defined legislation can be a positive aspect for further study.