1. Introduction
ata encryption is important to the security and integrity of information to be transmitted through a network. The need for a secured communication is more profound than ever, recognizing the fact that the conduct of almost all our business and personal matters are carried out today by computer networks [1]. Hence, in an environment where data encryption applications are fast-evolving, an algorithm that offers efficient and low-complexity encryption can provide security for information against intrusion and sophisticated threats that abound now. Moreover, the information that has to be transmitted must be encrypted to reduce the size of the data and increase processing speed.
As part of the information transmission, images are extensively used in such fields as desktop publishing, medical imaging, military target analysis, manufactured automation control, machine vision, geophysical imaging, graphic arts and multimedia [1]. The application of these image features is so dependent on the type of hardware required for high performance that very large scale integration (VLSI) technology becomes vital for digital image processing [2].
One method of designing high-speed and low power VLSI digital systems is by using the residue number system (RNS) [2]. The RNS has such inherent features as parallelism modularity, fault tolerance and carry-free propagation. These features make RNS widely used in Digital Signal Processing (DSP) application such as digital filtering, convolution, Fast Fourier Transform (FFT) and image processing [3], [4], [5]. Thus, RNS is the best tool to employ for a secured, fast and successful image data or image pixels or image elements encryption method.
A two-dimensional image function can be viewed as f(x,y), where x and y are spatial (plane) coordinates and f is the amplitude at any pair coordinate (x,y), called the intensity or gray level of an image at that point. When x,y and the amplitude values are all finite or discrete quantities, the object so formed is a digital image [6], [7].
In this paper, we present an image coding scheme which is based on the residue to binary converter for the three moduli set {2n+2,2n+1,2n} presented in [3]. The image coding scheme achieves speed and area in terms of security.
To clarify this framework, this study gives some background to the image processing scheme, which leads to the proposed coding techniques. The study concludes from an analysis of the encoding and decoding process.
2. II.
3. Backround
Images are coded and processed to produce results that are more secured and protected than the original images for specific applications. Hence the best approach for achieving a secured, high-speed and lowpower VLSI implementation for digital image coding and processing is by the use of the residue number system (RNS) [1], [2]. A residue number system is defined in terms of a relatively prime moduli set
n i i m ,... 1 } { = such thatL K W ? = as ) ,... , , ( 3 2 1 n w w w w W = , where i m i i i l k w ? =, for i=1,n. The complexity of the calculation of this operation ? is determined by the number of bits required to represent the residue and not by the one required to represent the input operands [3], [7], [8].
This RNS system achieves high speed computation because of its parallel computing nature. In order to convert numbers from binary to residue numbers, a residue-to-binary converter is required at the front end. Then, to convert back from residue to binary a residue-to-binary converter is required at the back end. The residue-to-binary converter usually consists of a lot of moduli operations; the computation of which is tedious. The reverse converter (residue-to-binary) is a crucial part of the RNS system. To perform the conversion of residue-to-binary, that is convert the residue number [10]. The traditional CRT is shown in equation ( 1):
) ,... , , ( 3 2 1 n x x x x into the binary number X, the traditional CRT is used [1][2][9],(
Where
? = = n i i m M 1 , , i i m M M = and 1 ? i M is the multiplicative inverse of i M with respect to i m . The moduli set, n i i m ,... 1 } { =, must be pairwise and relatively prime for the equation (1) to be used. In this case, the moduli set {2n+2, 2n+1,2n} has a common factor. This simply implies that for equation (1) to be used in the conversion back to binary the moduli set must be mapped to a set of relatively prime moduli. Hence the decimal conversion of ) ,... , , (
3 2 1 n x x x xfor the moduli set which are not pairwise relatively prime can be computed as follows [3], [6]:
(2)
1 L M n i i i x X ? = = ? Where L M is the Lowest Common Multiple (LCM) of n i i m ,... 1 } { =, the set of moduli sharing a common factor, X is the decimal equivalent of (3)
n i i x ,... 1 } { = , i1 1 L i L M n i i i i M x X ? = ? = µ ? ?Therefore, a software-based RNS image coding scheme has been proposed as a good tool in image data coding [1][2]. This paper codes the entire image data and so makes it more detailed and achieves a high-speed and low-power VLSI implementation.
4. III. Proposed image encription scheme
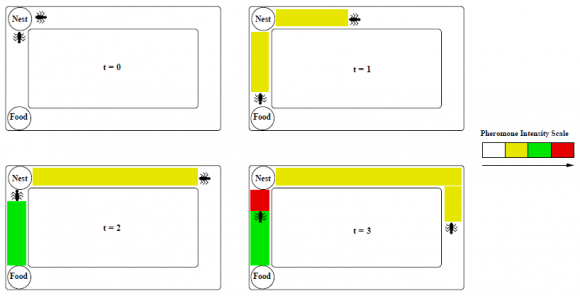
RNS can serve three goals, namely, to increase the speed of transmission, reduce the area of image data, and increase the security level of transmission through computer networks.
5. a) New Method for Image Data Coding
The image data coding system consists of an encoder and a decoder. The moduli set {2n+2, 2n+1,2n}, which has a common factor is used for the image coding scheme. The encoder is built by a R/B converter, which requires an RNS image processor of small wordlength. The decoder is used to recover the encrypted bitstream according to the moduli set and the proposed conversion technique in [3]. The modified RNS-to-Binary conversion method does not require the computation of a multiplicative inverse and also reduces the problem of the large modulo M as compared to the conversion using the traditional CRT. Considering the reduction in the large mod-M to mod-n and the elimination of the computation of the multiplicative inverse the proposed image coding scheme achieves reduced area, increased speed and decrease in internal delay of the conversion from RNS to binary.
6. b) Security of the Proposed Coding Scheme
Compared to the binary image coding, the proposed RNS image coding scheme has an encoder and a decoder, which is designed based on the operation of a three moduli set with a common factor. The end results of the RNS image encoder in this new scheme are in small-wordlength and are arranged into a certain encrypted order. An intruder who breaks into the network does not know the moduli set and the order of the encrypted bitstream that are computed in parallel. Only the designed decoder with the correct R/B converter and moduli set can recognize and decode the encrypted bitstream back to the processed and transformed digital image data according to the way they are arranged. The conversion was done using n=3, since the dynamic range of the grayscale image is 255, using the moduli set {2n +2, 2n + 1, 2n}, the moduli set will form {8, 7, 6}.
7. Encoder and decoder
The designed system is divided into two parts. The first part deals with the encoding that is mainly carried out by the encoder (B/R converter). The second part involves the decoding, which is implemented by the decoder (R/B converter). a) Encoder 1. Read the original digital image signal as binary or decimal value. 2. The digital image data or elements are encrypted into bitstream in a certain order according to the moduli set.
3. The encrypted bitstream is processed by the RNS image processor and the output is sent.
b) Decoder 1. The processed encrypted bitstream (digital image data encoded with RNS) is received and recognized. 2. The decoder with the correct moduli set is used to decode the encrypted bitstream back to binary or decimal so that it is easily read by the computer.
8. Conclusion
Data encryption is the process of transforming information (referred to as plaintext) using an algorithm (called a cipher) to make it unreadable to anyone except those possessing special knowledge, usually referred to as a key. The result of the process is encrypted information (in cryptography, referred to as cipher text). The reverse process, i.e. to make the encrypted information readable again is referred to as decryption, (i.e. to make it unencrypted).
In this paper, we built an encryption and decryption scheme based on a three moduli set. We demonstrated the security strengths of the encryption scheme. The proposed scheme outperforms most of the encryption schemes in terms of area and delay due to the fact that our scheme operates on smaller magnitude operands as it requires less complex adders and multipliers, which potentially offers high-speed processing.

![The proposed scheme achieves high-speed and low-power VLSI implementation for image processing such as digital image transform and digital image filtering. The design of the scheme is based on the residue to binary converter presented in[1] as shown below:Theorem 1: Given the moduli set](https://computerresearch.org/index.php/computer/article/download/536/version/100471/2-Modeling-a-Secured-Digital-Image-Encryption_html/6993/image-3.png)

![Convert the encrypted pixel bitstream from RNS-to-Binary using the proposed technique in[1]. Where n = 3.](https://computerresearch.org/index.php/computer/article/download/536/version/100471/2-Modeling-a-Secured-Digital-Image-Encryption_html/6996/image-6.png)
| 154 | 153 | 155 | 155 | 153 | 154 | 154 | 155 | 154 | 152 | 155 | 154 |
| 156 | 156 | 157 | 155 | 153 | 155 | 155 | 154 | 156 | 156 | 158 | 157 |
| 156 | 159 | 160 | 154 | 153 | 155 | 153 | 155 | 155 | 156 | 157 | 156 |
| 158 | 161 | 157 | 158 | 157 | 157 | 159 | 155 | 156 | 157 | 160 | 159 |
| 159 | 161 | 158 | 159 | 160 | 161 | 156 | 155 | 156 | 158 | 158 | 156 |
| 156 | 158 | 157 | 160 | 158 | 158 | 158 | 156 | 154 | 156 | 157 | 156 |
| 158 | 158 | 158 | 156 | 157 | 157 | 154 | 154 | 155 | 153 | 152 | 155 |
| 156 | 155 | 155 | 153 | 156 | 154 | 155 | 154 | 153 | 157 | 153 | 153 |
| 155 | 155 | 154 | 154 | 157 | 157 | 156 | 155 | 158 | 160 | 158 | 157 |
| 156 | 159 | 158 | 159 | 157 | 157 | 155 | 157 | 160 | 158 | 156 | 158 |
| 157 | 157 | 157 | 159 | 156 | 156 | 156 | 157 | 160 | 159 | 156 | 158 |
| 153 | 156 | 158 | 158 | 160 | 157 | 156 | 158 | 159 | 159 | 156 | 156 |
| 2 | 1 | 3 | 3 | 1 | 2 | 2 | 3 | 2 | 0 | 3 | 2 |
| 4 | 4 | 5 | 3 | 1 | 3 | 3 | 2 | 4 | 4 | 6 | 5 |
| 4 | 7 | 0 | 2 | 1 | 3 | 1 | 3 | 3 | 4 | 5 | 4 |
| 6 | 1 | 5 | 6 | 5 | 5 | 7 | 3 | 4 | 5 | 0 | 7 |
| 7 | 1 | 6 | 7 | 0 | 1 | 4 | 3 | 4 | 6 | 6 | 4 |
| 4 | 6 | 5 | 0 | 6 | 6 | 6 | 4 | 2 | 4 | 5 | 4 |
| 6 | 6 | 6 | 4 | 5 | 5 | 2 | 2 | 3 | 1 | 0 | 3 |
| 4 | 3 | 3 | 1 | 4 | 2 | 3 | 2 | 1 | 5 | 1 | 1 |
| 3 | 3 | 2 | 2 | 5 | 5 | 4 | 3 | 6 | 0 | 6 | 5 |
| 4 | 7 | 6 | 7 | 5 | 5 | 3 | 5 | 0 | 6 | 4 | 6 |
| 5 | 5 | 5 | 7 | 4 | 4 | 4 | 5 | 0 | 7 | 4 | 6 |
| 1 | 4 | 6 | 6 | 0 | 5 | 4 | 6 | 7 | 7 | 4 | 4 |
| 0 | 6 | 1 | 1 | 6 | 0 | 0 | 1 | 0 | 5 | 1 | 0 |
| 2 | 2 | 3 | 1 | 6 | 1 | 1 | 0 | 2 | 2 | 4 | 3 |
| 2 | 5 | 6 | 0 | 6 | 1 | 6 | 1 | 1 | 2 | 3 | 2 |
| 4 | 0 | 3 | 4 | 3 | 3 | 5 | 1 | 2 | 3 | 6 | 5 |
| 5 | 0 | 4 | 5 | 6 | 0 | 2 | 1 | 2 | 4 | 4 | 2 |
| 2 | 4 | 3 | 6 | 4 | 4 | 4 | 2 | 0 | 2 | 3 | 2 |
| 4 | 4 | 4 | 2 | 3 | 3 | 0 | 0 | 1 | 6 | 5 | 1 |
| 2 | 1 | 1 | 6 | 2 | 0 | 1 | 0 | 6 | 3 | 6 | 6 |
| 1 | 1 | 0 | 0 | 3 | 3 | 2 | 1 | 4 | 6 | 4 | 3 |
| 2 | 5 | 4 | 5 | 3 | 3 | 1 | 3 | 6 | 4 | 2 | 4 |
| 3 | 3 | 3 | 5 | 2 | 2 | 2 | 3 | 6 | 5 | 2 | 4 |
| 6 | 2 | 4 | 4 | 6 | 3 | 2 | 4 | 5 | 5 | 2 | 2 |