1. INTRODUCTION
-government is about bridging government and citizen communications in more efficient, transparent and reliable ways through effective use of information technology. With the increasing use of Information technology, functions in government and businesses are now increasingly dependent on network of critical information infrastructure. As such, any disruption of the operation of information systems of critical infrastructure is likely to have a devastating effect on people, departmental records, economy, essential human & government services and national security. And also brings back to normality, it takes time.
The Internet has become the main media for egovernment from delivering public information to electronic document and financial transactions although it is widely attributed to serious security weaknesses. As a result, security and privacy are the most crucial concerns of any e-government applications. In the view of the potential impact, protection of critical information infrastructure is essential to ensure that disruptions are infrequent, of minimal duration & manageable and cause the least damage possible. Users of information resources must have skills, knowledge, and training to manage information resources, enabling the organizations to effectively serve the customers/users through automated means. Personnel with program delivery responsibilities should recognize the importance of security of information resources and their management to mission performance.
Ensuring security of e-government applications and infrastructures is crucial to maintain trust among in between departments to store, process and exchange information over the e-government systems. Due to dynamic and continuous threats on e-government information security, policy makers need to perform continuous evaluation on existing information security practices and controls. Based on the fact, this paper attempts to propose a holistic approach from managerial decision making perspective by combining all related aspects of security to create a framework used to evaluate e-government security strategy.
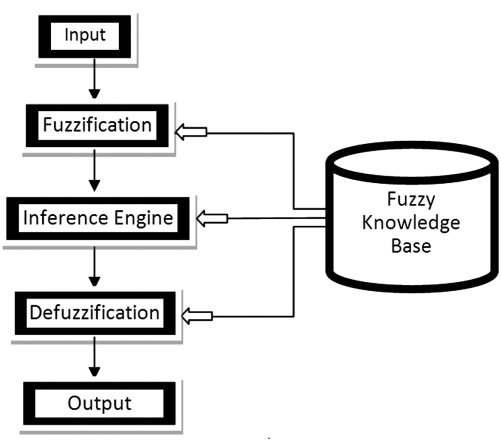
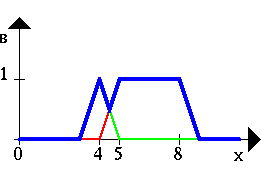
2. Figure : Input to Output Fuzzification process
There are many factors which account for the increase in question but the most prominent among them is the rapidly growing use of soft computing and especially fuzzy logic in the conception and design of intelligent systems .As one of the principal constituents of soft computing, fuzzy logic is playing a key role in the conception and design of various systems. There are two concepts within fuzzy logic which play a central role in its applications. The first is that of a linguistic variable, i.e., a variable whose values are words or sentences in a natural or synthetic language. The other is that of a fuzzy
( D D D D ) Gif-then rule in which the antecedent and consequent are propositions containing linguistic variables. The essential function served by linguistic variables is that of granulation of variables and their dependencies. In effect, the use of linguistic variables and fuzzy if-then rules results -through granulation in soft data compression which exploits the tolerance for imprecision and uncertainty. In this respect, fuzzy logic mimics the crucial ability of the human mind to summarize data and focus on decision-relevant information Since decision making mostly involve fuzzy logic techniques and alternative to consider altogether, this framework implement fuzzy logic techniques approach to view e-government security strategy from managerial perspective. Fuzzy set theory is applied to complement the framework in order to capture fuzziness in the form of inconsistencies and vagueness coming from subjective judgments by decision makers.
3. II.
4. METHODOLOGY
Fuzzy Logic introduced by Zadeh (1965) gives us a language, with syntax and local semantics, in which we can translate our qualitative knowledge about the problem to be solved. Fuzzy logic is a powerful problem-solving methodology with a myriad of applications in embedded control and information processing. Fuzzy provides a remarkably simple way to draw definite conclusions from vague, ambiguous or imprecise information. In a sense, fuzzy logic resembles human decision making with its ability to work from approximate data and find precise solutions.
5. Straight line
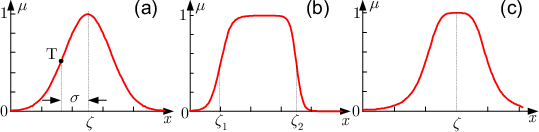
The simplest membership function is formed by straight line. We consider the speed of car fig (1.1), and plot the membership function for high. Where the horizontal represent the speed of the car and vertical axis represent the membership value for high.
ii.
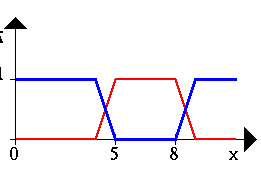
6. Trapezoidal
If we consider the case 1.2 and plot the membership function for "less", we get a trapezoidal membership function.
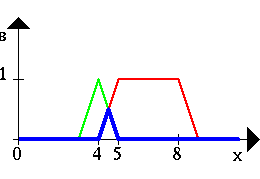
7. Triangular
This is formed by the combination of straight lines. The function is name as "trimf" .We considers the above case i.e. fuzzy set Z to represent the "number close to zero". So mathematically we can also represent it as The FIS editor handles the high level issuing for the system such as the number of input and output variables an their names, types of the 'AND' and 'OR' operators, and the aggregation and defuzzification methods.
0 if x<-1 ?z(x) = x + 1 if -1 ? x <0 (1.4) 1 -x if 0 ? x <1 0 if 1? xi.
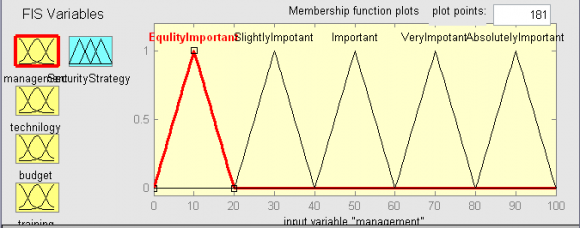
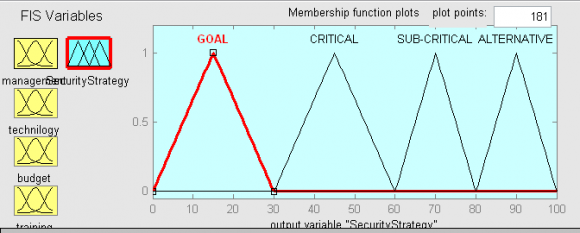
8. The member ship function editor
The membership function editor is used to define the properties of the membership function for the systems variables.
ii.
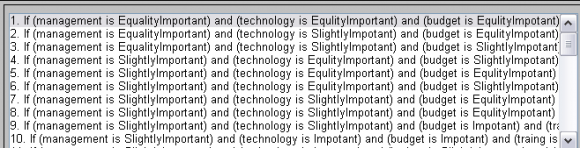
9. The rule editor
The rule editor enables the user to define and edit the of rules that describe the behavior of the system.
iii.
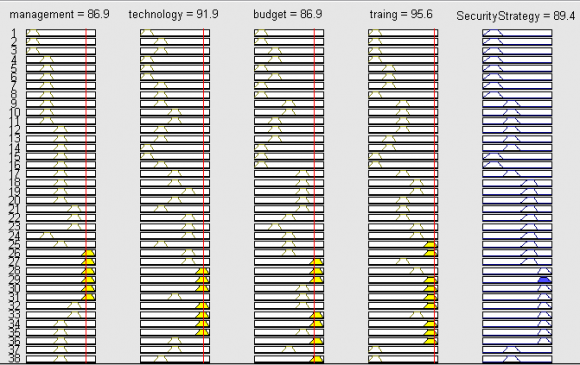
10. The rule viewer
The rule viewer is a read only tool that displays the whole fuzzy inference diagram. iv.
11. The surface viewer
The surface viewer is also a read only tool. it is used to display how an output is dependent on any one or two of the inputs.
In this topic researcher work is to develop a methodology fuzzy logic theory is used here, because this theory is more appropriate for this type of problem.
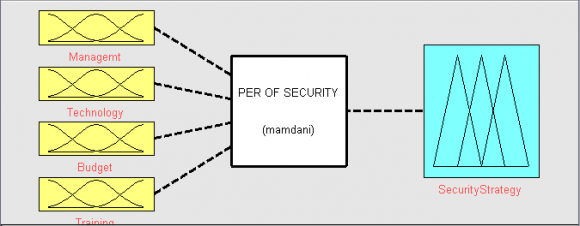
Various factors for evaluate the performance will considered. We will consider most relevant some of the factors selected and will be fuzzified as input fuzzy variable "performance will be fuzzified with suitable fuzzy linguistic variable, and ultimately FIS will be developed.
12. RULE
As per the input and output parameters fuzzified as shows rule base is generated by applying my own reasoning as an expert person to observe or taking decision to Evaluate the performance security strategy of a There are 34 numbers of rules generated using 'AND' and 'OR' operator. The overall rules are written below. The following table shows that how inference engine works for different input values .if we observe this table minimally then one can say that for different values of a input parameters the output (performance) that is produced by FIS more or less current.
13. VII. Comparision Table
Comparative In the above table an example is demonstrated by and my point of view is taking arranging input values for getting the output as security performance in shape triangular and trapezoidal member ship we get the result same.
14. VIII.
15. Conculsion
In this research paper we tried to developed the security strategy for E-Governance of the government by using fuzzy logic expert system because each and every government department need the absolutely flaw less performance of the security strategies, and using fuzzy technology evaluation of security strategies on the basis of various key performance attributes that have been validated. For obtaining the desired level of performance, we take input value for various attributes applied different membership functions and applied to the same linguistic variables, triangular and trapezoidal, more of less similar and compared the performance and we got the performance of absolute security parameters. The fuzzy scale has been designed to map and control the input data values from absolute truth to absolute false. The qualitative variables are mapped in to numeric results by implementing the fuzzy export system model through various input examples and provide a basis to evaluate government system security strategy.



| Fuzzy inference system editor |
| 2012 |
| 26 |
| Volume XII Issue X Version I |
| D D D D ) G |
| ( |
| Global Journal of Computer Science and Technology |
| Srl. No. MANAGEMENT | TECHNOLOGY | BUDGET | TRANING | TRIANGULAR | |
| 1 | 9.78 | 12.5 | 18 | 17.3 | 20.6 |
| 2 | 15.8 | 16.9 | 17.3 | 19.8 | 38.7 |
| 3 | 32.1 | 29.4 | 38.1 | 30.6 | 50 |
| 4 | 64.1 | 68.1 | 70.6 | 69.4 | 70 |
| 5 | 71.9 | 84.4 | 88.1 | 85.6 | 90.6 |
| D D D D ) G |
| ( |